



This article is a sub-topic under Virtualization Technology: Empowering Ethical Hackers And Red Teams For Cybersecurity Excellence
In the ever-evolving landscape of cybersecurity, the need for agile and scalable hacking infrastructure has become paramount. Ethical hackers, red teams, and penetration testers require a dynamic and adaptable environment to effectively simulate real-world cyberattacks, assess vulnerabilities, and fortify defenses. This article delves into the key strategies and considerations for building an agile and scalable hacking infrastructure that empowers cybersecurity professionals to conduct comprehensive assessments and stay ahead of evolving threats.
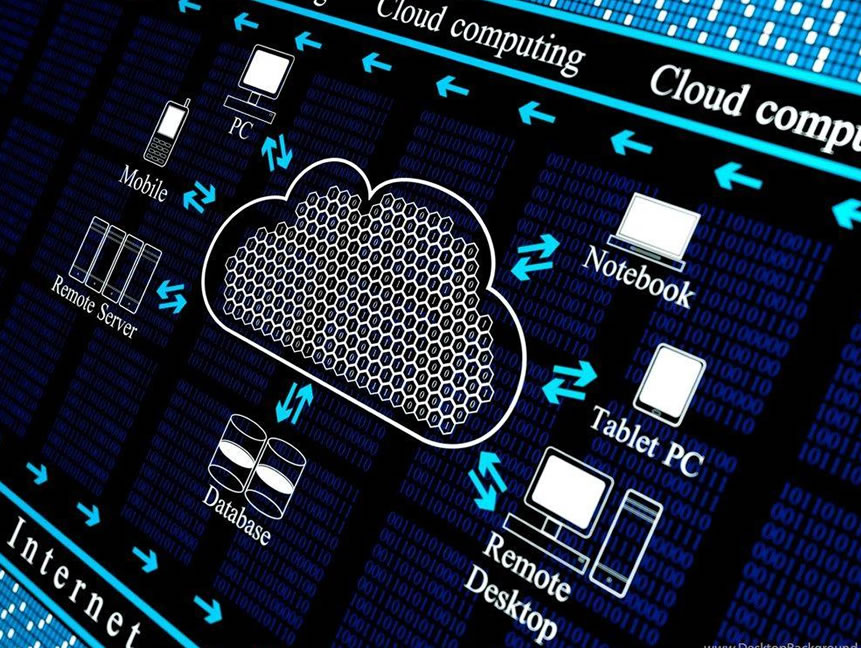
**1. Cloud-Based Virtualization:
Leveraging cloud-based virtualization platforms offer unparalleled scalability. Cloud services allow hackers to spin up virtual machines on demand, enabling the creation of multiple testing environments without the limitations of physical hardware. This flexibility is particularly valuable for large-scale assessments, as resources can be provisioned and de-provisioned as needed.
**2. Orchestration and Automation:
Orchestration tools streamline the management of virtual environments, making it easier to deploy, configure, and control multiple instances. Automation scripts can set up predefined testing scenarios, allowing testers to focus on analyzing results rather than repetitive setup tasks. By scripting routine processes, ethical hackers can enhance efficiency and reduce the time required for assessments.
**3. Containerization:
Containers provide a lightweight and consistent environment for applications. By containerizing hacking tools and services, cybersecurity professionals can quickly deploy isolated instances without concerns about compatibility or resource overhead. This approach facilitates portability and allows for the easy transfer of environments between different systems.
**4. Modular Architecture:
Designing a modular architecture for your hacking infrastructure enhances flexibility. Divide your infrastructure into functional modules, such as reconnaissance, exploitation, and post-exploitation. Each module can be independently scaled and customized based on the requirements of specific assessments, ensuring an efficient allocation of resources.
**5. Dynamic Resource Allocation:
Modern hacking infrastructures should embrace dynamic resource allocation. Cloud-based environments can be scaled up during intensive testing phases and scaled down when not in use. This adaptive approach optimizes resource utilization and reduces costs while maintaining the agility to respond to changing assessment demands.
**6. Version Control and Documentation:
Maintaining version control for hacking tools, scripts, and configurations is essential. Changes can be tracked, tested, and rolled back if necessary. Documentation of the infrastructure setup, configurations, and workflows ensures continuity and facilitates collaboration among team members.
**7. Security Considerations:
An agile and scalable hacking infrastructure must prioritize security. Implement robust access controls, firewalls, and encryption mechanisms to prevent unauthorized access. Regularly update and patch all components to address vulnerabilities and ensure that the infrastructure remains secure.
**8. Scalable Data Management:
Effectively managing the data generated during assessments is crucial. Use scalable data storage solutions, such as cloud-based databases, to store findings, logs, and other relevant information. This ensures that critical insights are accessible and organized for analysis and reporting.
**9. Training and Knowledge Sharing:
An agile infrastructure should accommodate training and knowledge sharing. Create sandboxed environments for educational purposes and allow team members to experiment with new tools and techniques. Regular knowledge-sharing sessions can enhance the expertise of the entire team.
Conclusion:
An agile and scalable hacking infrastructure empowers ethical hackers, red teams, and penetration testers to conduct comprehensive assessments and adapt to evolving cyber threats. By embracing cloud-based virtualization, automation, containerization, and modular design principles, cybersecurity professionals can build an infrastructure that meets the demands of modern cybersecurity challenges. This approach not only enhances the efficiency and accuracy of assessments but also positions organizations to proactively defend against emerging threats. Building an infrastructure that is both agile and scalable is not just a strategy; it’s a blueprint for cybersecurity excellence in an ever-changing digital landscape.
Read More
1. Virtualization and the Ethical Hacker’s Playground: Explain how virtualization creates a secure playground for ethical hackers and red teams to practice their craft. Discuss the benefits of isolating testing environments and utilizing virtual snapshots for quick recovery during intensive hacking exercises.
2. Unleashing the Red Team: Real-World Simulations through Virtualization: Explore how red teams use virtualization to conduct real-world simulations of cyberattacks. Discuss the strategic value of creating diverse virtual scenarios to identify vulnerabilities, assess risks, and enhance an organization’s overall cybersecurity posture.
3. The Role of Virtual Machines in Penetration Testing: Highlight the significance of virtual machines in penetration testing. Discuss how ethical hackers leverage VMs to perform penetration tests on various operating systems and applications while keeping the production environment safe from unintended consequences.
4. Building an Agile and Scalable Hacking Infrastructure: Guide ethical hackers and red teams on building an agile and scalable hacking infrastructure using virtualization. Discuss the benefits of cloud-based virtualization and orchestration tools in managing larger-scale engagements and assessing complex network topologies.
5. Virtualization and C2 Servers: Navigating the Nexus of Control and Security: Amidst this dynamic environment, the fusion of virtualization and Command and Control (C2) servers emerges as a critical nexus, offering both enhanced control and strengthened security measures
6. The Future of Virtualization for Ethical Hackers and Red Teams: Look ahead to the future of virtualization technology and its potential impact on the evolving landscape of ethical hacking and red teaming. Discuss how virtualization will continue to evolve to meet the growing demands of the cybersecurity industry.

Web Developer | Cybersecurity Advocate | Offensive Security Enthusiast
Passionate about Personal Transformation and Offensive Security, I’m Ehinomhen Okaiwele—a dedicated Web Developer and Cybersecurity Advocate. My mission is clear: elevating the “Cybersecurity Consciousness” of fellow Africans. Through my journey, I aim to empower individuals, fostering a safer digital landscape for our community. Join me in this transformative endeavor.